So, what exactly is an information technology security audit? Forget the dreaded exam stereotype. Think of it as a strategic health check for your company's digital nervous system, engineered to deliver a clear business outcome. It’s a methodical, expert review of your entire information system, benchmarking your security against recognised standards to prove your platform is enterprise-ready.
This isn't just a quick technical scan. With our high-energy, proactive approach, we treat it as a deep dive into your security posture to hunt down vulnerabilities, crush regulatory requirements, and shield the assets that drive your revenue.
Turn Your IT Security Audit into a Growth Engine
Let's get something straight. Most leaders see an information technology security audit as a pure hassle—an expensive, time-sucking distraction from the real work of building a business. That reactive mindset is a direct anchor on your growth. We operate from a consulting mindset: a security audit isn't a cost; it's a powerful business accelerator, a hidden lever for growth that creates incredible, measurable value.
This goes way beyond just dodging fines or avoiding a PR nightmare. A proactive audit is a direct investment in your brand's reputation and, most importantly, in the trust your customers place in you. It's time to shift security from a reactive chore into a forward-thinking, competitive advantage that fuels your bottom line.
From Compliance Hurdle to Competitive Edge
Embracing our #riteway methodology is all about taking Extreme Ownership of your security. It’s not an isolated problem to palm off to the IT department; it’s a shared, strategic responsibility. When you get it right, it builds serious momentum across the entire business. A properly executed audit is a powerful signal to the market—and your stakeholders—that you’re mature, capable, and ready to win at the enterprise level.
This forward-looking stance has a real, measurable impact on your business outcomes:
- Building Unshakeable Customer Trust: Being able to prove your platform is secure is a massive sales tool, especially when you're courting those larger enterprise clients who demand it.
- Protecting and Sustaining Revenue: By finding and fixing vulnerabilities before they're exploited, you prevent breaches that could halt operations, destroy trust, and send customers running.
- Attracting Investor Confidence: A rock-solid security posture proves to investors that your platform isn't just a great idea—it’s resilient and built to scale safely, taking a huge amount of risk off the table and increasing valuation.
A proactive audit turns security from a cost centre into a revenue enabler. It's the ultimate proof point that your platform is not just innovative, but also stable, trustworthy, and ready for enterprise-level success.
The Stark Reality for UK Businesses
If you need more convincing, the data speaks for itself. The UK government's latest Cyber Security Breaches Survey found that a staggering 43% of UK businesses suffered at least one cybersecurity breach in the last year alone. Phishing was the weapon of choice, accounting for a massive 93% of incidents against businesses. The threat is real, and having robust security is non-negotiable for survival and growth. Exploring a free cyber security audit can be a smart first step to understanding your current risk exposure.
When you transform your approach with a high-energy, proactive partner, you give your team the confidence to scale fearlessly, innovate faster, and dominate your market. This is how you align your security strategy with your most critical business goals, a concept we explore further in our guide to high-impact product development software.
Choosing the Right Audit for Your Business Goals
Let's be honest, picking an information technology security audit isn't a simple tick-box exercise. Get it wrong, and you've just torched a pile of cash, wasted valuable engineering hours, and probably missed a huge opportunity. Getting it right means turning a security task into a genuine business accelerator that delivers a clear return on investment.
This isn't about collecting certifications for vanity. It’s about being incredibly strategic. Are you trying to crack the enterprise market and land those six-figure deals? Compliance audits are your key. Are you more concerned about whether your platform can actually fend off a real-world attack? Then you need to be looking at technical assessments.
We live and breathe this stuff. Our #riteway approach is all about zeroing in on the exact audit that gives you the biggest bang for your buck, transforming a security line item into a powerful tool for winning customers and driving revenue.
Audits for Building Trust and Winning Deals
For any SaaS business, certain audits are basically a passport to bigger and better markets. They’re not just about checking your security posture; they're powerful trust signals that scream to big customers, "We're a safe pair of hands."
SOC 2 (Service Organisation Control 2): This is the undisputed heavyweight champion for SaaS companies, especially in the US. A clean SOC 2 report is a business asset that proves you have your act together when it comes to managing client data. It tells prospects that your controls for security, availability, processing integrity, confidentiality, and privacy are bulletproof.
ISO 27001: Think of this as the global standard for managing information security. Bagging an ISO 27001 certification shows you have a serious, risk-based system for protecting sensitive information. It's a massive advantage when you're up against competitors for international business or clients in heavily regulated fields.
Think of these audits as a direct investment in your sales pipeline. They answer all the tough security questions before the procurement team even asks them, which can slash your sales cycle and unlock deals you simply couldn't touch before. Of course, a big part of the planning is figuring out how much a SOC 2 audit costs, as that will definitely influence your timeline and budget.
Audits for Fortifying Your Fortress
While compliance audits open doors, technical audits make sure those doors are actually locked and barred. It’s one thing to have the blueprints for a fortress; it’s another to hire a team to actively try and smash the walls down. That’s what technical audits do—they give you raw, unfiltered feedback on your real-world defences.
Your security posture is only as strong as your weakest link. Technical audits find those links before an attacker does, transforming theoretical risks into actionable remediation tasks that strengthen your entire infrastructure.
These audits get you out of the world of policies and into the trenches, testing your actual code and infrastructure. And it all starts at the foundation—having strong software architecture design principles is absolutely crucial for passing these hands-on assessments.
Matching the Audit to Your SaaS Business Objective
To make the decision a bit clearer, think about what you’re trying to achieve as a business. This table breaks it down nicely.
| Audit Type | Primary Business Goal | Best For |
|---|---|---|
| SOC 2 | Win enterprise deals and build trust with US-based clients. | SaaS companies storing or processing sensitive customer data. |
| ISO 27001 | Expand into global markets and demonstrate mature security governance. | Companies targeting international customers or regulated industries. |
| Vulnerability Scan | Quickly identify known security weaknesses in your systems. | Regular, automated health checks to maintain security hygiene. |
| Penetration Test | Simulate a real-world attack to find exploitable vulnerabilities. | Validating the effectiveness of your security controls before a launch. |
Making the right choice means putting your security budget where it will have the biggest impact on your bottom line. It’s all about being smart, proactive, and laser-focused on the business outcome you want.
The Proactive Audit Lifecycle Playbook
A successful information technology security audit isn't won during the testing phase. It's won long before the auditors even walk through the door. Viewing an audit as a last-minute scramble is a recipe for derailed roadmaps and painful remediation cycles. That's a reactive approach, and we reject it entirely.
With a high-energy, proactive mindset, the audit lifecycle becomes a predictable, value-adding process. It’s a rhythm that strengthens your platform instead of stressing your team. This isn't just about passing a test; it's about building a resilient, secure foundation for growth. It requires a consulting mindset, where every step is deliberate and laser-focused on a clear business outcome.
Let's break down the playbook for mastering each critical phase, transforming a compliance headache into a powerful operational advantage.
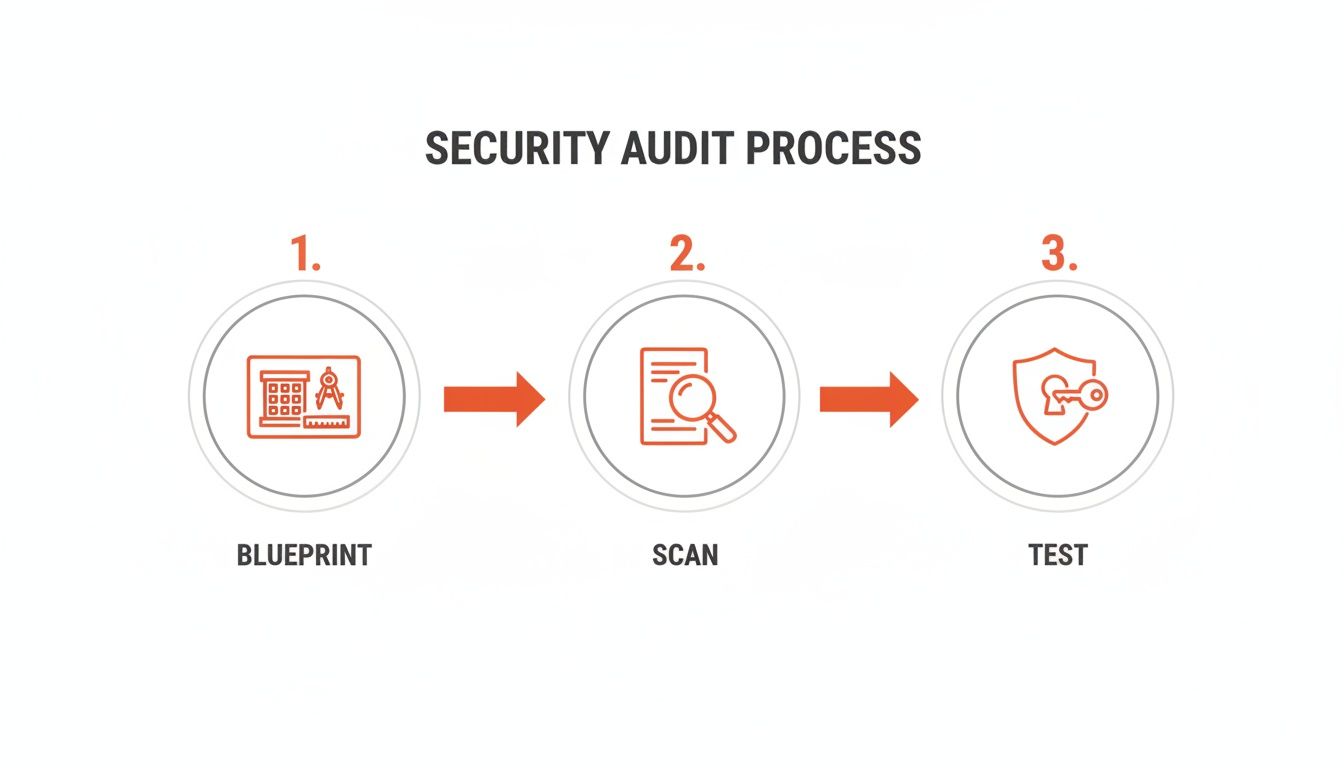
This simple visualisation shows the core flow of a proactive security audit process, moving from initial planning to active testing.
The key takeaway is that each stage builds on the last. A rock-solid blueprint is absolutely essential for efficient scanning and effective testing.
Blueprint Your Success With Strategic Scoping
The first and most critical phase is scoping. Get this wrong, and you'll waste countless hours collecting irrelevant evidence or, even worse, miss a critical vulnerability that comes back to bite you. Scoping isn't about boiling the ocean; it's about drawing a razor-sharp perimeter around what truly matters to your business.
We sit down with you to define the audit's boundaries based on your real-world objectives. Are you targeting enterprise clients? Then the scope must include every system handling their data. Launching a new feature? That needs to be ring-fenced and scrutinised. This proactive alignment ensures the audit focuses its energy where the risk—and the business value—is highest.
Master the Flow of Evidence Collection
Next up is evidence collection. This is where so many audits get bogged down in chaos. Auditors start requesting logs, policies, and configuration files, sending engineering teams on a frantic scavenger hunt. Our approach treats this as a managed process, not a fire drill.
We help you establish a "single source of truth" for all your audit artefacts. By organising documentation and automating data gathering wherever possible, we turn a reactive, painful task into a smooth, repeatable workflow. This organised approach not only impresses auditors but, more importantly, frees up your best engineers to focus on building your product.
An audit should be a reflection of your everyday security practices, not a frantic, staged performance. When evidence collection is seamless, it proves your security culture is real, active, and deeply embedded in your operations.
And don't forget the supply chain. Third-party involvement in breaches recently doubled to around 30%, with vulnerability exploitation rising 34% year-over-year. Shockingly, only 54% of perimeter device vulnerabilities were fully remediated. This makes the case for rigorous evidence collection across your entire ecosystem, not just your own code.
Uncover Actionable Insights With Rigorous Testing
With a clear scope and organised evidence, the testing phase becomes an exercise in validation, not panicked discovery. This is where auditors examine your controls, run their scans, and try to find weaknesses. Because we've prepared proactively, there are far fewer surprises and the findings are much more constructive.
The goal here isn't to get a perfect score. It's to uncover actionable insights that make you stronger. A finding isn't a failure; it's a gift—an opportunity to harden your defences before a real attacker finds the same weakness.
From Technical Jargon to Business Impact Reporting
A great audit report doesn't just list vulnerabilities; it translates technical findings into clear business risks. This is where a strategic partner truly shines. We make sure the reporting phase produces a document that empowers leadership to make smart, informed decisions.
Instead of a 100-page document filled with jargon, you get a prioritised action plan. Each finding is framed in the context of business impact: "This vulnerability could lead to a data breach affecting our top ten customers," not "CVE-2023-XXXX requires patching." This clarity is absolutely crucial for securing the resources you need for remediation.
Accelerate Growth With Integrated Remediation
Finally, we arrive at remediation. For many companies, this is where the audit report goes to die, buried under a mountain of new feature requests. Not with us. We transform remediation from a painful delay into a rapid, integrated part of your development sprints.
By embedding security directly into your workflow, we ensure that fixing vulnerabilities is treated with the same urgency as shipping new code. This is fundamental to building a truly secure platform and is a core component of our philosophy on integrating security into the software development lifecycle. This proactive stance ensures your audit delivers lasting value, strengthening your platform and accelerating your growth.
Using Compliance Frameworks to Win Enterprise Deals
If you're a SaaS business with big ambitions, landing enterprise clients is the name of the game. It's how you unlock that next level of growth. But here’s the thing about these bigger players: their tolerance for risk is practically zero. They won't just take your word for it that their data is safe—they need to see cold, hard proof.
This is exactly where compliance frameworks like SOC 2 and ISO 27001 become your secret weapon in the sales process.
Forget seeing them as bureaucratic box-ticking exercises. Think of them as a universal language of trust. They instantly tell a potential enterprise customer, "We get it. We take your security as seriously as you do." Suddenly, an information technology security audit isn't a cost centre; it's a high-octane fuel injection for your sales engine.
Our whole philosophy is built on this. We don’t just drag you through an audit. We get in the trenches with you, helping turn that certificate into a powerful market differentiator that closes bigger deals, faster.
From Checkbox to Competitive Advantage
Let’s be blunt: a SOC 2 report or an ISO 27001 certification can be the single deciding factor in a seven-figure deal. Imagine a big corporation's procurement team weighing up their options. When they see a vendor with verifiable security controls, that vendor immediately leaps to the top of the pile.
It’s that simple. And the results are incredibly tangible:
- You'll shorten sales cycles. You’ve already answered the exhaustive security questionnaire before they even think to send it. That's a massive roadblock instantly cleared from the sales path.
- You'll unlock entirely new markets. Many global enterprises and government bodies won’t even begin a conversation with a vendor that lacks an ISO 27001 certification.
- You can justify premium pricing. Proven security is a premium feature. It gives your sales team the confidence—and the evidence—to stand firm on your price point against cheaper, less secure rivals.
Choosing Your First Framework Strategically
You don’t need to boil the ocean and tackle every framework at once. The real key is being strategic. Your first major compliance push should be laser-focused on your most critical business goals. This is where our consulting mindset comes in—we help you pick the path that delivers the biggest, fastest return on your investment.
SOC 2 (Service Organisation Control 2)
This is, without a doubt, the gold standard for SaaS companies targeting the US market. It’s all about proving you have robust operational controls for handling customer data, measured against criteria like Security, Availability, and Confidentiality. A clean SOC 2 report is a powerful seal of approval.
ISO 27001
Now, if you’re looking globally, ISO 27001 is the international benchmark for an Information Security Management System (ISMS). It's less about ticking off specific controls and more about demonstrating a comprehensive, risk-based system for managing security. For breaking into Europe or regulated sectors like finance, it's absolutely essential.
A compliance certificate is so much more than a piece of paper. It's a strategic asset that proves your security maturity, builds instant trust with large clients, and gives you an undeniable edge over the competition.
GDPR: The European Market-Access Requirement
While it's not a certification you can hang on the wall, General Data Protection Regulation (GDPR) compliance is non-negotiable for any company that handles the data of EU citizens. A solid GDPR programme shows you respect user privacy and is a foundational requirement for doing business in Europe. You can be sure that enterprise buyers will put your GDPR posture under the microscope.
So, where do you start? It all comes down to your target market. If you're chasing those big US-based enterprise logos, SOC 2 should be your priority. If your growth plan is all about Europe and global expansion, then ISO 27001 is the logical first step. By taking this business-first approach, you guarantee your information technology security audit efforts are perfectly aligned with your most important growth goals.
The Classic Audit Pitfalls (And How to Dodge Them)
Even the most well-intentioned IT security audit can fall flat. When audits go off the rails, it’s almost never because of some super-complex technical glitch. The real culprits are the same old predictable, avoidable mistakes in planning and mindset. They’re the silent killers of ROI, turning what should be a valuable exercise into a frustrating, costly distraction.
We’ve seen these patterns play out time and time again. But here’s the good news: with a bit of foresight and the proactive #riteway methodology, you can sidestep every single one. Getting this right transforms the audit from a painful slog into a smooth process that genuinely protects your business and helps it grow.
Pitfall #1: Defining a Scope Without a Purpose
The quickest way to waste time and money on an audit? Treat the scope like a technical to-do list. When the scope is vague or way too broad, your teams will spend weeks chasing down irrelevant data while the systems that actually matter get overlooked. An audit without a clear business objective is just noise.
This is why we always start with the "why." Are you trying to land that big enterprise deal? Then your scope needs to be laser-focused on the systems protecting customer data. Are you proving your resilience to nervous investors? Then your core infrastructure and disaster recovery plans have to be front and centre.
A successful audit scope isn't defined by technical boundaries, but by business outcomes. It answers the question, "What are we trying to prove, and who are we proving it to?" That clarity is everything.
Pitfall #2: No Real Backing from the Top
Here’s another classic mistake: the audit is seen as just an "IT problem." Without genuine buy-in from the C-suite, the whole process lacks urgency and authority. Your engineering teams are left trying to beg for resources and push for changes without the top-down support they need, which just leads to friction and endless delays.
True Extreme Ownership means security is treated as a leadership-level responsibility. When your executives are actively championing the audit, it sends a powerful message across the entire organisation: this matters. It guarantees that remediation gets prioritised and the audit's findings lead to real improvements, not just a report that gathers dust on a shelf.
Pitfall #3: Treating It Like a Once-a-Year Exam
So many companies treat their annual audit like a final exam you can cram for. They scramble to get things in order, breathe a sigh of relief when it's over, and then immediately go back to their old habits. This "snapshot" approach to security is incredibly risky because it leaves you wide open for the other 11 months of the year.
Think about it: an audit should be a reflection of your everyday security posture, not a staged performance for the auditors. When you build security controls and continuous monitoring into your daily operations, the audit just becomes a simple validation of the great work you're already doing. This state of continuous readiness is what separates the mature, resilient companies from everyone else. The market gets it, too. The UK Cyber Security Sector's contribution rocketed to £13.2 billion in the last financial year, a 12% jump, which shows just how massive the demand is. You can dig into the numbers in the latest sectoral analysis report.
Pitfall #4: Finding Problems with No Plan to Fix Them
Finally, the most common failure of all is finishing an audit without a clear, resourced plan to fix what you found. An audit report filled with critical findings is completely useless if you have no strategy to act on them. Remediation isn't an afterthought; it needs to be planned and budgeted for right from the start.
A good partner helps you translate those audit findings directly into your development backlog, prioritising the fixes based on actual business risk. This proactive approach makes remediation an integrated part of your workflow, ensuring that every insight from your information technology security audit makes your platform stronger and more resilient.
How a Strategic Partner Accelerates Audit Readiness
Getting ‘audit-ready’ can feel like hitting the emergency brake on your entire product roadmap. It’s a familiar, painful story. Suddenly, your best engineers are pulled from creating value to hunt down documentation and patch legacy systems. It's a reactive scramble that kills momentum for months.
But it absolutely doesn’t have to be this way.
A strategic nearshore engineering partner is your ultimate accelerator. They can transform audit readiness from a disruptive, all-hands-on-deck emergency into a natural, predictable outcome of your development process. It's about shifting from last-minute panic to a state of continuous compliance, freeing your team to focus on what they do best: building an amazing product.
Build Security In, Don't Bolt It On
The old way of thinking is to build features first and worry about security later. This approach always leads to a massive, expensive clean-up project right before an information technology security audit. We reject that model completely. With our product-first mindset, we don’t just write code; we build secure, compliant platforms from day one.
Our senior teams integrate security controls directly into the CI/CD pipeline. This means every new feature is built with the audit requirements already in mind. This proactive approach makes readiness a simple by-product of your everyday workflow, not a separate, painful project.
We believe in Extreme Ownership. Audit readiness isn't someone else's problem—it's a shared responsibility baked into every sprint. By making security a foundational part of the development lifecycle, we ensure you’re always prepared, eliminating the last-minute fire drills.
From Technical Debt to Tangible Value
A true strategic partner does more than just follow orders; they act as a proactive consultant, flagging risks long before an auditor ever sees them. Our high-energy teams are trained to spot potential compliance gaps and security weaknesses as they work, turning potential audit findings into simple backlog tickets.
This proactive mindset converts a reactive, costly exercise into a value-generating activity. By continuously addressing security and compliance, we help you:
- Ship features faster and with confidence, knowing they are built on a secure foundation.
- Pass audits predictably, with fewer surprises and a much smoother overall experience.
- Stay focused on your core business goals, without your roadmap being hijacked by compliance demands.
Instead of seeing an information technology security audit as a barrier to growth, you can view it as a simple checkpoint. With the right partner, readiness isn't a project you manage; it's a capability you own.
Frequently Asked Questions
Got questions about IT security audits? We've got answers. Here’s a quick rundown of what SaaS founders and engineering leaders often ask us.
How Long Does an IT Security Audit Take?
Honestly, it depends on the business outcome you're driving towards. A simple vulnerability scan might wrap up in a few days, but if you're aiming for a heavy-hitter like SOC 2 or ISO 27001, you're looking at a journey that can last anywhere from three to twelve months.
Think of it in stages. Strategic planning takes a solid 2-4 weeks, and gathering all the evidence can stretch from 4-12 weeks. Then, the auditors get to work with active testing, which adds another 2-6 weeks. The secret sauce? Having a partner who bakes security into your development from day one. It drastically cuts down the time you spend scrambling to get ready and fix issues, keeping you in a state of constant preparedness.
What Is the Average Cost of an IT Security Audit?
The price tag is tied directly to the audit's scope and the size of your operation. For a typical mid-sized SaaS company, a targeted penetration test will likely land between £5,000 and £15,000.
When you step up to major compliance frameworks, a SOC 2 Type 1 report can range from £15,000 to £30,000, while getting certified for ISO 27001 often starts around £20,000. It's crucial to view this not as a cost, but as an investment in revenue growth.
The real ROI from a security audit isn't just a certificate to hang on the wall. It's measured in the enterprise deals you win, the crippling data breaches you avoid, and the boost to your company's valuation.
Can We Prepare for a Security Audit Internally?
You absolutely can, but it's a huge trade-off. Going it alone demands a massive amount of time and energy from your best people, pulling senior engineers away from what they do best: building your product. This isn't a small task; it involves a full readiness assessment, a painstaking gap analysis, and then building a plan to fix everything. Innovation often grinds to a halt for months.
This is where a strategic partner changes the game. Our high-energy teams take Extreme Ownership of the entire process—handling the technical fixes, the process tweaks, the documentation—so your team can keep their foot on the gas, shipping features and delighting customers.
Ready to turn your next audit into a launchpad for growth? At Rite NRG, we build secure, compliant, and scalable platforms that don't just pass audits—they ace them. This frees up your team to focus on what truly matters. Discover how our approach can accelerate your roadmap.